Most organizations know they have computers, websites, and email accounts. Fewer know the full extent of everything connected to their business online. Many things can exists outside of what you think you may be managing, including accidental leaks, shadow IT, forgotten vendors, outdated websites, abandoned cloud storage, and misconfigured systems.
Whether you’re trying to get a handle on public files that shouldn’t be public, preparing for a penetration test, meeting insurance expectations, or simply reducing risk, a proper digital asset inventory is one of the smartest places to start.
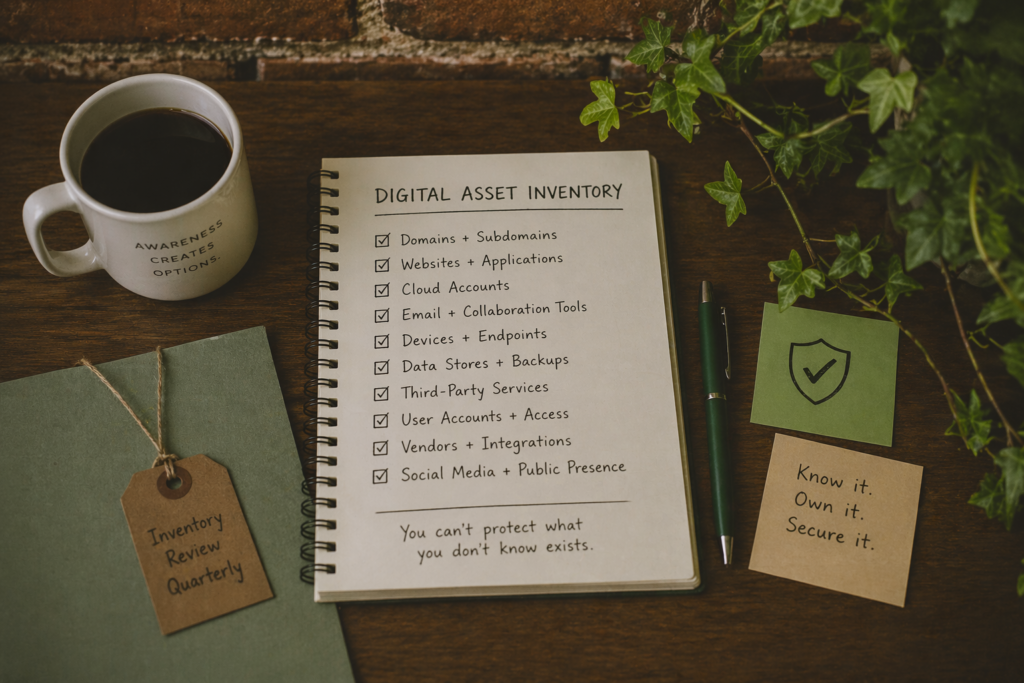
At Applied Awareness, we view asset inventory as practical situational awareness. You cannot secure what you do not know exists. If an attacker, investigator, journalist, or automated scanner can find a neglected system before you can, that system becomes part of your risk profile whether you intended it or not.
What Is a Digital Asset Inventory?
A digital asset inventory is a structured record of the systems, accounts, services, domains, data stores, and technology resources connected to your organization. This includes obvious assets such as your main website, laptops, and Microsoft 365 tenant, but also less obvious items such as old domains, third-party SaaS tools, social media pages, backup files, vendor portals, development environments, public file shares, and forgotten subdomains.
Think of it as creating a map of your organization’s digital footprint. Some assets are officially managed. Others may still exist because they were created years ago, inherited through staff turnover, or spun up quickly to solve a short-term problem and never retired properly.
Why This Matters
Many security issues are not caused by advanced hacking. They come from ordinary neglect. Think of the following scenarios:
- A former contractor’s admin account still active.
- An old website running outdated plugins.
- A public cloud bucket containing invoices.
- A test login page indexed by search engines.
- A DNS record pointing to a service nobody uses anymore.
These issues can lead to data leaks, reputational damage, fraud, ransomware access paths, or failed pentest findings. They can also create insurance complications if an organization cannot demonstrate reasonable control over its environment.
A strong asset inventory helps with:
- Preventing accidental public exposure
- Identifying forgotten systems before attackers do
- Preparing for vulnerability scans or pentests
- Supporting cyber insurance questionnaires
- Improving incident response readiness
- Reducing vendor and third-party risk
- Creating accountability for ownership and maintenance
Start With What You Know
You don’t have to be an expert in cybersecurity or investigations to get started.
Begin by listing the assets everyone already expects to see. Your primary domain names, websites, office computers, mobile devices, servers, routers, business software, email platforms, and cloud subscriptions—these should all be documented.
For each asset, record:
- Name of asset
- Purpose
- Owner or responsible person
- Vendor or platform
- Internet-facing or internal only
- Sensitive data involved
- Current status (active, dormant, retired)
- Authentication method
- Recovery method
- Backup status
- Last reviewed date
This does not need to be fancy. A spreadsheet is often enough to start.
Then Look for What You Forgot
This is where many inventories become valuable. The second phase is discovery. Search for what may still be tied to your organization but missing from internal records.
Check for:
- Old domains still registered under the business
- Subdomains such as dev, test, portal, staging, mail, vpn, oldsite
- Legacy websites or campaign microsites
- Social media pages created by past staff
- Third-party tools billed to company cards
- Cloud storage links shared publicly
- Old SaaS accounts with dormant users
- Public documents indexed by search engines
- Exposed backups or archive files
- Vendor systems connected to your brand or data
This is where OSINT thinking becomes useful. Search engines, certificate transparency logs, DNS records, archived websites, and passive discovery tools can often reveal assets organizations forgot existed.
Include Data Exposure Paths
Asset inventory should also cover where your information lives, not just where your hardware sits. Make sure to include all locations such as:
- Microsoft 365 / Google Workspace
- Shared drives
- Dropbox / Box / OneDrive
- CRM platforms
- Accounting software
- HR systems
- Marketing tools
- Backup repositories
- Vendor portals
- Staff devices storing business files
Ask a simple question: if sensitive files were accidentally made public tomorrow, where would they most likely come from?
Make Ownership Explicit
One of the biggest operational failures is the “someone must be handling that” problem. Every critical asset should have a named owner responsible for access reviews, patching, renewals, and lifecycle decisions. If nobody owns it, it usually drifts.
Ownership does not always mean technical administration. It means accountability.
Review It Regularly
Asset inventories become stale quickly. Staff leave, subscriptions change, domains renew, vendors are added, and temporary solutions become permanent.
Review the inventory on a schedule:
- Quarterly for growing organizations
- Before renewing cyber insurance
- Before a pentest
- After mergers or acquisitions
- After major staff turnover
- After incidents or suspicious findings
Even a modest annual review is better than none.
It’s Not About How Big You Are
Many smaller organizations assume they are too small to worry about this. In practice, smaller businesses, municipalities, nonprofits, contractors, and family-run companies often have the most organic environments: years of practical fixes, inherited logins, mixed vendors, and limited documentation.
That does not mean failure. It means the environment likely evolved faster than governance did. An asset inventory is how you catch up.
Final Thoughts
Cybersecurity often begins with visibility, not tools. Before buying another product, before booking a pentest, before your next breach event, make sure you know what you actually have. Your digital footprint may be larger than expected, and risk often hides in what was forgotten rather than what was attacked.
At Applied Awareness, we aim to provide free knowledge and resources to help organizations identify unmanaged exposure, understand their real-world digital footprint, and build practical security foundations that match reality.
For a full listing of paid engagements we can support you with, check out our services page.
